To evaluate Azure Event Hubs functionality, typically we need to develop an application for data ingestion and another for data consumption
In my previous blog post, I outlined the process of discovering ingested data in Event Hubs using Azure Data Explorer. In this article, I will demonstrate how to ingest data into Event Hubs without writing a single line of code.
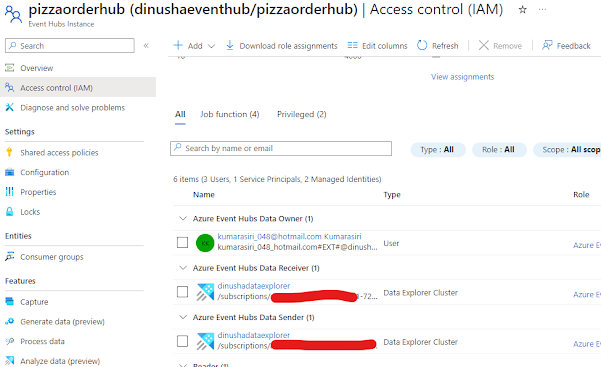
Our first step is to navigate to the Event Hubs instance and access the Generate data (preview) feature.
Multiple options are provided to ingest payload either from pre-canned datasets or custom payloads based on a given schema.
Then, you can easily discover this data in your pre-configured Azure Data Explorer. I have detailed the steps involved in configuring Azure Data Explorer in my previous blog post.
This approach allows you to explore the functionality of Event Hubs without writing any code!